Digital Learning Platform

A unique learning experience
The Institute of Information Security (IIS) has developed a Digital Learning Platform (DLP) to meet the growing demand for cybersecurity skills in the industry. The DLP provides a unique learning experience, allowing users to learn at their own pace and convenience with pre-recorded lectures, online labs, exams, quizzes, and assignments.
The platform offers a wide range of courses covering various topics in information security, structured in modules, and includes regular feedback and assessments to help students track their progress.

An all-in-one solution
With easy registration and course navigation, the DLP offers a seamless user experience. Users have access to a personalized dashboard that gives a clear overview of their progress, while interactive features such as quizzes, simulations, and case studies help users apply their knowledge in real-world scenarios. The platform caters to students, working professionals, and aspiring cybersecurity experts who seek to enhance their knowledge and skills in information security.
This all-in-one solution offers comprehensive course content, expert guidance, and a variety of support and resources to make the learning experience seamless and enjoyable, making it the ideal platform for anyone looking to upskill in cybersecurity.
Create your free account
Short term Courses: For professionals
The course covers fundamental aspects of security in a modern networked environment with the focus on system design aspects in the specific context of network / internetwork security. It provides information that the participants can apply directly when they go back to work.
The Operating Security course includes everything important you need to know to secure your systems running Microsoft Windows and Linux. This training will show you how each Windows security and Linux security technology works, how to access vulnerabilities and secure your information.
This course focuses on implementing security in databases by using controls and various security features in order to protect the data.It includes database hardening concepts along with other security requirements.,
The course covers advanced aspects of security in a modern networked environment with the focus on system design aspects in the specific context of network / internetwork security. It provides information that the participants can apply directly when they go back to work.,
This course is for all web app developers, testers, designers who wish to improve their security skill. Developers and System Architects wishing to improve their security skills and awareness. Including Team Leaders and Project Managers, Security practitioners and managers and Auditors.
This course is focusing on Security Enthusiasts, IT professionals, and Mobile Application Developers seeking to understand typical mobile application security issues in detail.
The Certified Professional Hacker NxG is a revolution in the field of information security training. It goes far beyond the usual courses that talk about the same old port scanning and vulnerability assessments. It goes deep down into the depths of networking, systems, web applications and actual exploitation.
The Certified Cybersecurity Expert is a completely hands-on, real-world oriented security certification. This course is designed by experienced security professionals focusing on delivering the best and updated knowledge, and ensures that you get personally mentored by the best in the business. The upside of joining this program is that you will be able to cover a wide variety of topics, starting from the basics, and then leading up to compliance standards, and even digital forensics and cybercrime investigations.
The term cyber-crime no longer refers only to hackers and other external attackers. Almost all every case of financial fraud or employee misuse involves a very strong element of computer-based evidence. This entire course is driven by hands-on exercises and case studies to ensure that all aspects have a real-life scenario-based approach.,

This course covers concepts of cryptography, steganography and Malwares.

This course covers compliance standards and concepts such as Information security management system, business continuity management and payment card industry data security standards.
In this Course, we are going to learn about common cloud misconfigurations, how to perform a risk assessment and verify compliance for various Cloud Services. Further, we will delve deeper into identifying security risks in these cloud services and to implement best practices to mitigate the common cloud misconfigurations. Also, we will jumpstart into the compliance aspect based on well known standards like NIST, OWASP, Cloud Security Alliance etc, along with their automations.

This course will present security guidelines and considerations in wireless networking. The participants will learn the latest security standards, including all 802.1x/EAP types used in WLANs , how to locate and triangulate rogue access points and implement Wireless Intrusion Prevention Systems, assess the security of wireless networks using the same hacking tools the bad guys do.
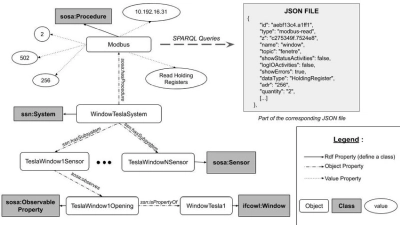
"Exploiting IoT" is a unique course designed to offer you the ability to evaluate the security of these smart devices. This course is ideal for those wanting to understand the security issues associated with IoT and enabling them to make better decisions when building, deploying and assessing IoT technologies

This course cover ISMS concepts including framework and other concepts regarding the information security management system.,

This course is designed to introduce the PCI DSS family of standards, and then do a deep-dive into the 12 Requirements and each control.

This course aims at imparting knowledge on implementation techniques in addition to gaining an understanding of the framework.,
This course cover GDPR concepts including principles , rights of data subjects etc.
This course cover HIPAA concepts including safeguards and other requirements.,

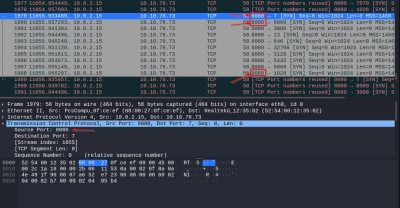
This course help you to understand the netwrok traffic flow and how to find different artifactes through pcap newtrok capture file and its analysis.,

This course help you to understand the different process involved in malware infection of windows system,
.webp)
This course focuses on identifying and managing risks through developing, implementing and maintaining the information security controls.It includes all the four domains and their details.
This comprehensive module includes solid foundational components for an organization's overall information security awareness program. It improves the understanding of key people in the organization about information security risks, sound information protection practices, and how their individual actions and behaviors can impact information security in their organization.
This comprehensive module includes solid foundational components for an organization's overall information security awareness program . It improves the understanding of key people in the organization about information security risks, sound information protection practices, and how their individual actions and behaviors can impact information security in their organization.
This exceptional course uses a stimulating and creative approach that engages and challenges the learner. Interactive learning activities and realistic scenarios are presented that maintain interest and add relevance for learners from different departments and key responsibilities within the organization.
This comprehensive module includes solid foundational components for an organization's overall information security awareness program from Management perspective. It improves the understanding of key people in the organization about information security risks, sound information protection practices, and how their individual actions and behaviors can impact information security in their organization. This exceptional course uses a stimulating and creative approach that engages and challenges the learner. Interactive learning activities and realistic scenarios are presented that maintain interest and add relevance for learners from different departments and key responsibilities within the organization.
This course will present the guideline on Blockchain Development with the consideration of security of all components from development to bring in use blockchain application. This cover security best practices to be followed in each phase of blockchain development. The course revolves around testing and recommendation on weaknesses of application.,

This course is made far most in-depth crash course for freshers. It includes Frontend web technology using HTML. There are mini projects and code samples and by the end of this course participants should be able to call as a HTML designer and that's make someone by comfortable working with front end technology. Even participants should be able to create user interfaces with HTML applications.
This is the most complete Basic JavaScript course .It's an all-in-one package that will take the participants from the very fundamentals of JavaScript, all the way to building modern and complex applications. We will learn JavaScript from the very beginning, step-by-step. Based on the guidance, participants will go through practical and fun code examples, important theory about how JavaScript works behind the scenes, and beautiful and complete projects.
APIs are revolutionizing the modern Internet. As the complexities of APIs increase, software companies need skilled technical writers who can document them. This course will cover documenting structured data, which is the foundation of web API documentation and its talking about how structured data works then will dive into the format called JSON, showing both how to create JSON and how to document it. Finally, some of the tools that can use to create high quality documentation.
This course introduces the concept of malware, how they function, their types and how they are extensively used in Advanced Persistent attacks (APT's) to siphon off the critical business information from an organization on regular basis. We start off with the concepts of Assembly language, PE Header, disassembling v/s debugging with advanced debugging features. We also perform RE to analyze an application dissecting it to the level where malware code is present.
This course helps to Understand the Metasploit Exploitation Framework and Advance exploitation using Metasploit. Along with to extend the Metasploit framework with custom exploit/modules.,
In this course, We are going to learn from the basics of Advanced Nmap. Different types of scanning techniques. Bypassing firewall rules, Timing Options. Nmap output forms. Nmap Scripting Engine. This course ideal for Network Administrators and Pen testers.

This course will provide an understanding to the participants how Mobile Device Management (MDM) solutions secure, monitor, manage and support mobile devices which are used by the employees and managers. With the deployment of MDM solutions, participants shall witness how easy it becomes to enforce BYOD policy and comply with local laws and trans-border regulations across the enterprise. We shall look how MDM solutions optimize the functionality and security of a mobile communications network while minimizing cost and downtime.
This course focuses on social engineering techniques and reconnaissance used in penetration testing.,

This course focuses on enumeration and exploitation concepts and covers techniques for exploiting vulnerabilities.,

This Course is designed for beginners to learn the basic concepts of Core Java. Here participants will learn the fundamentals of Core Java (Class, Interface etc.)
Long term Courses: For beginners
The CISC course is designed to make our participant an expert in the domain of cybersecurity. CISC covers a wide variety of topics, starting right from the basics, and then leading up to compliance standards, and even forensics and cybercrime investigations.
The CCA is the only completely hands-on, real-world oriented security certification. It is a course designed by security professionals, and for security professionals. The content is updated very regularly in accordance to the requirements of this dynamic industry.
CGRC Part 1 covers a wide variety of topics, starting right from the basics covering Cyber security fundamentals,network security,server security & web application security concept.CGRC Part 2 provide participants with an understanding of all the globally accepted GRC frameworks and how they can be applied to drive higher levels of business performance and improve short, medium and long-term business sustainability.
The CSOC (Cybersecurity Operations Centre) allows an organization to enforce and test its security policies, processes, procedures and activities through one central platform that monitors and evaluates the effectiveness of the individual elements and the overall security system. This course will cover the design, deployment and operation of the CSOC. Once this course is completed, you will have the skills to perform your SOC responsibilities effectively.This course will help you to gain the skills to analyse and detect threats to an organization through demonstrations, labs, and lectures. The course covers the functional areas: Communications, Network Security Monitoring, Threat Intelligence, Incident Response, Forensics, and Self-Assessment.
Get certified
Comprehensive Support and Resources
Subscriptions
- 30+ Courses
- Excludes CISC Certification
- 30 Days Access
- 8/5 Support
- Non Refundable
- 30+ Courses
- Excludes CISC Certification
- 365 Days Access
- 8/5 Support
- Non Refundable
Testimonials
Our DLP has received positive feedback from our users, including students and professionals. Here are some testimonials from our users:
designation
designation
designation




.webp)














.webp)
.webp)